A satellite project of labs.iximiuz.com - an indie learning platform to master Linux, Containers, and Kubernetes the hands-on way 🚀
Ivan on the Server Side
|
Hello 👋 Ivan's here with a monthly roundup of all things Linux, networking, containers, and Kubernetes. What I was working onApril was a busy and fruitful month. The Hands-On Docker Roadmap 2.0After several weeks of thinking about it, I couldn't help but revamp the Docker roadmap. A plain SVG worked fine when the roadmap had only a few dozen links, but now it points to over 100 challenges and tutorials, so a more structured UX was very much needed. And it can now ping you, so you don't break the streak. Check out the recording - this time it's easier to show than tell: New Playgrounds: Kubernetes 1.36, Ubuntu 26.04, Fedora 44Keeping iximiuz Labs playgrounds up to date is one of my key priorities. This month's upgrade includes:
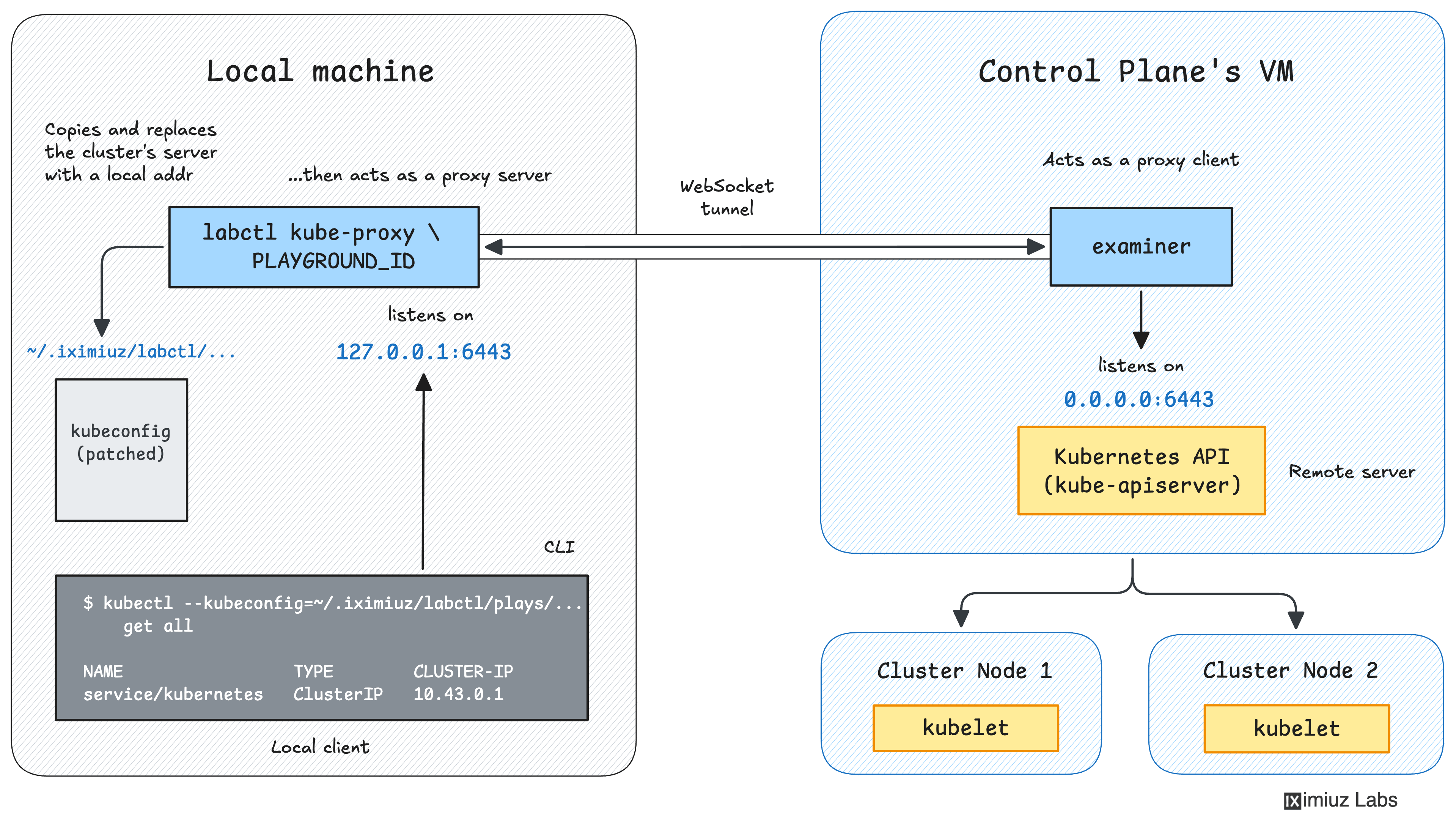
New Playground Features: Nested Virtualization and 24h UptimeA quick recap of the playground features released earlier this month. iximiuz Labs has finally received support for nested virtualization via the new Cloud Hypervisor-powered microVM backend. You can activate it either in the UI (on every playground's front page) or using the Why is it a big deal? Because now you can experiment with all the shiny sandbox solutions without polluting your local system - Firecracker, Docker's sbx, Kata Containers, and many more can now run in iximiuz Labs playgrounds. All paid-tier playgrounds had their memory limit increased from 8GB to 10GB (hopefully enabling some local LLM use cases), and it is now also possible to set a max playground uptime of up to 24 hours. Last but not least, building kernel modules and experimenting with software that requires kernel headers installed has become way easier - thanks to the new "dev" kernel variants that include the headers for the custom kernel versions iximiuz Labs uses. New LabCTL FeaturesConnecting to Kubernetes clusters running in playgrounds is now easier with the new
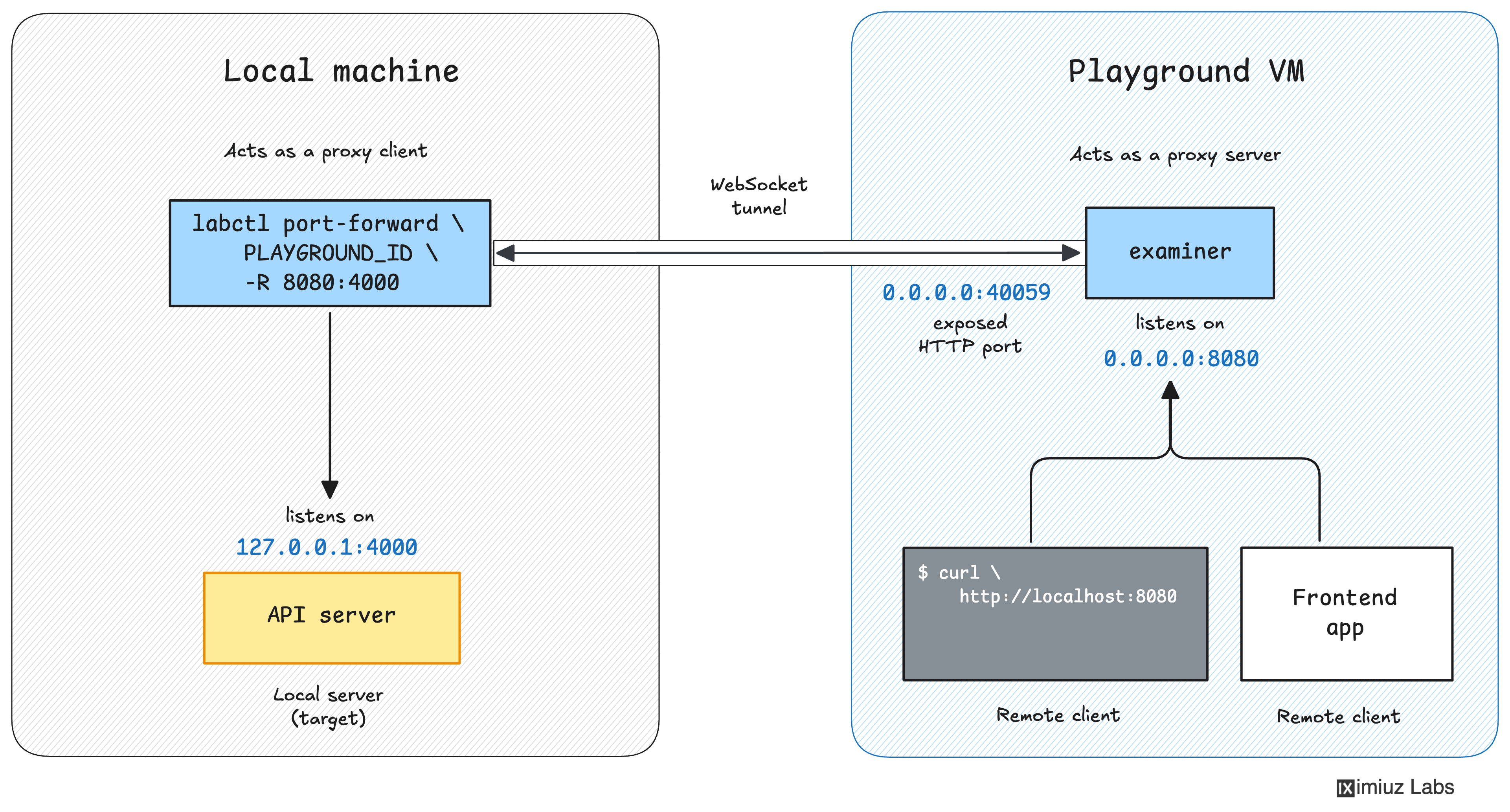
It has also become possible to securely expose TCP services running on your local machine to the playground VM using the
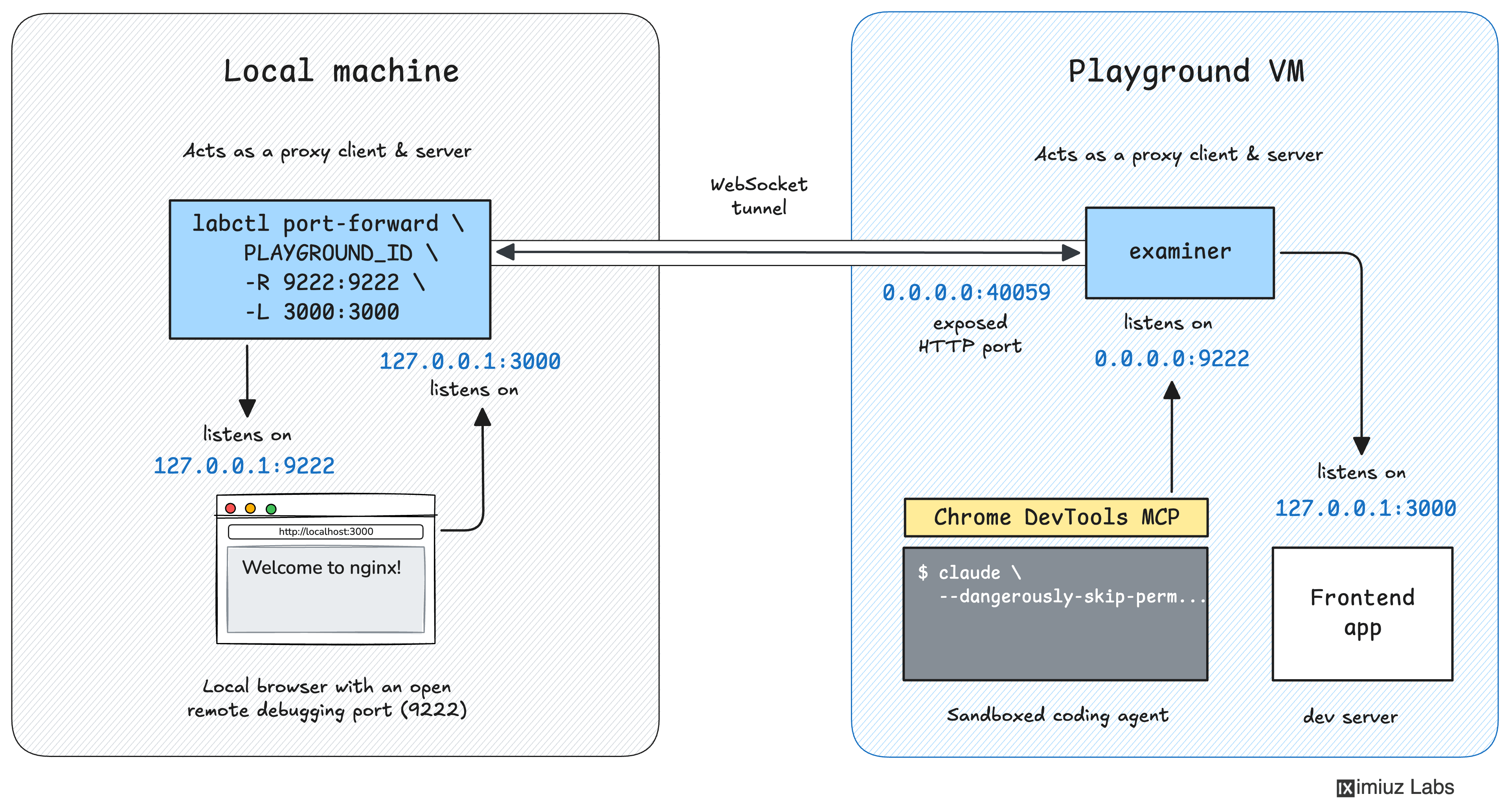
Remote port forwarding comes in handy when you need to make a service running on your local machine (on the intranet) accessible for services running in the remote playground. For example, you can use it to expose Chrome's debugging port (9222) to a coding agent running in the sandbox VM.
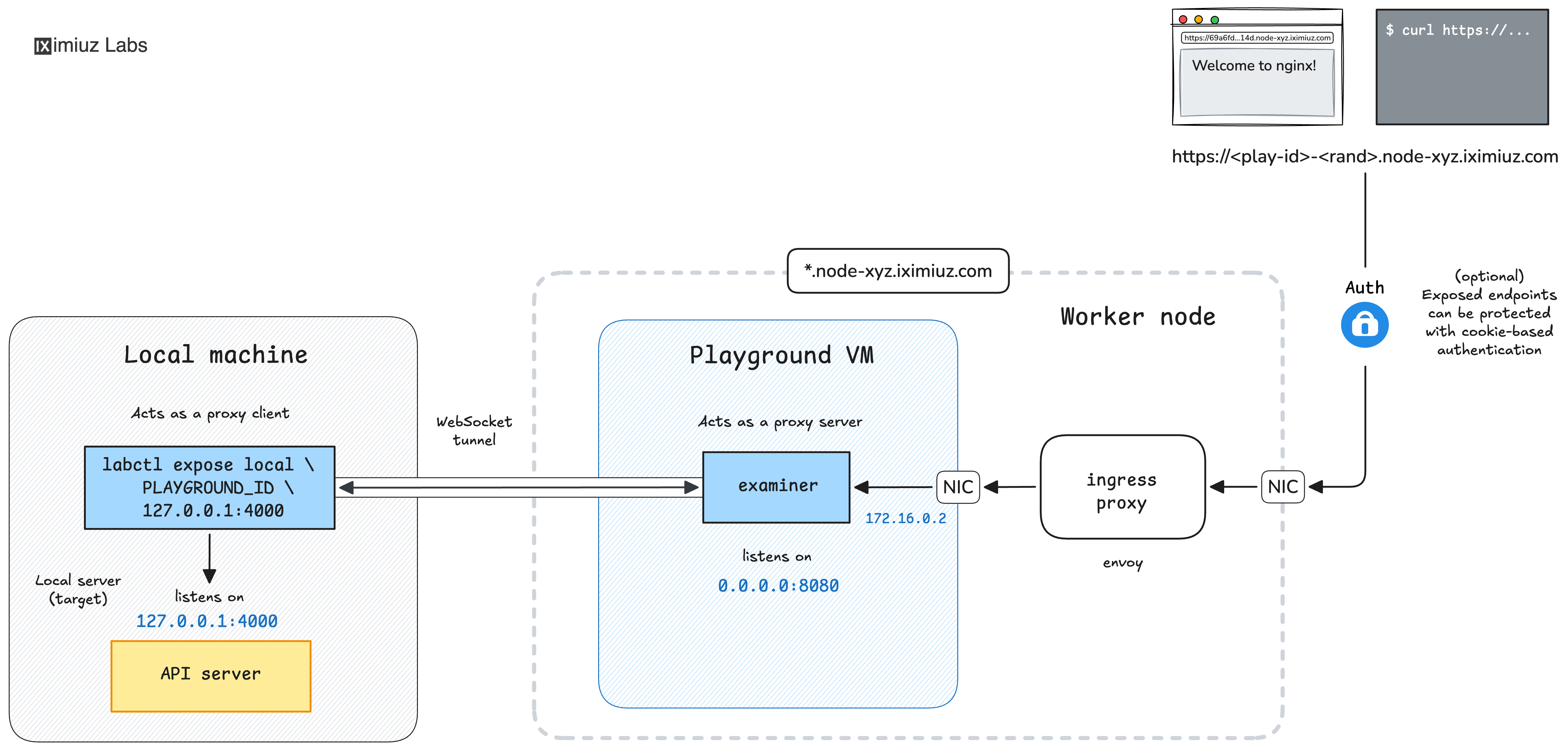
Lastly, even though it's not a key use case for iximiuz Labs playgrounds, you can now expose HTTP(S) services running on your local machine to the internet with
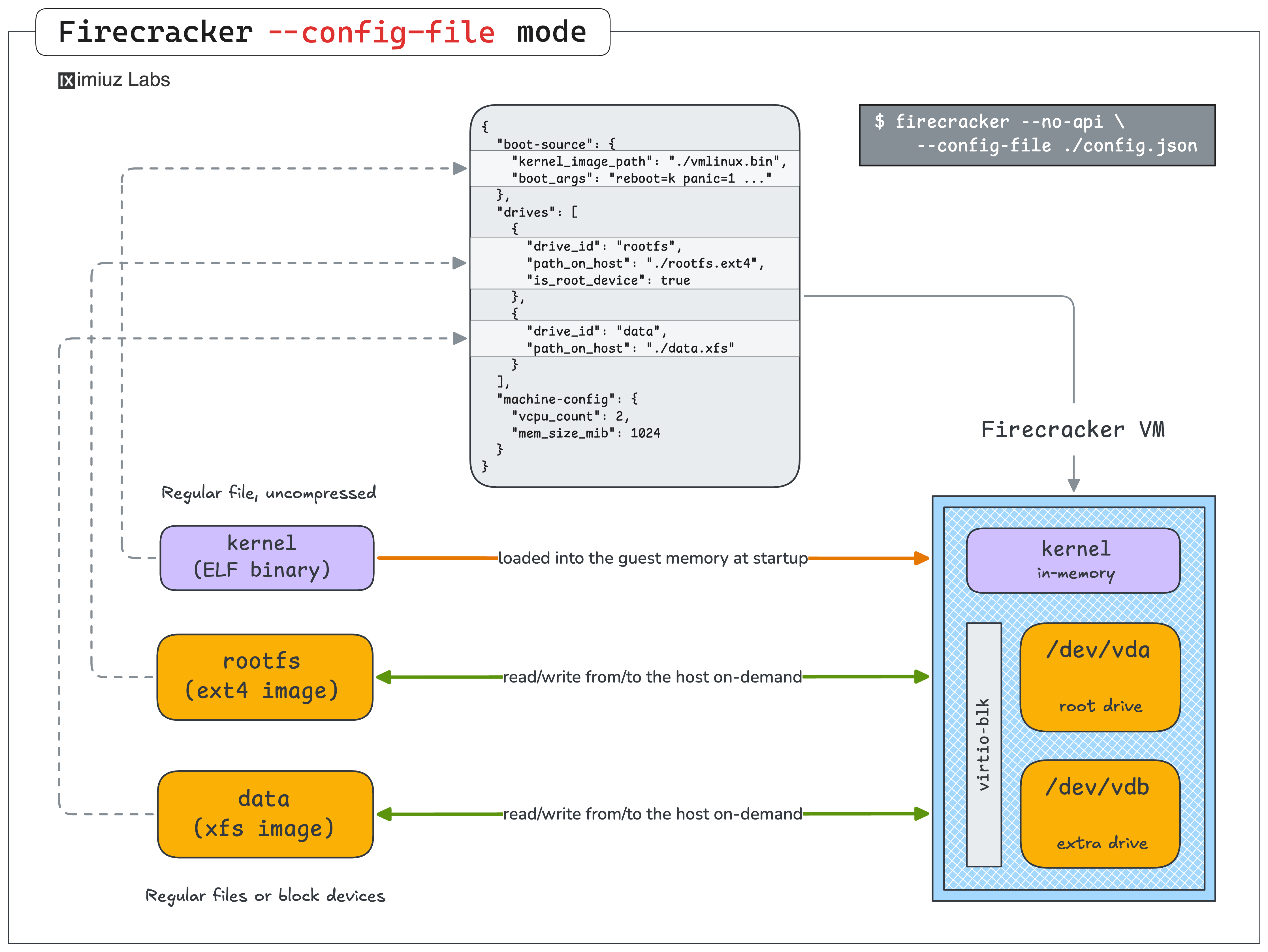
New Linux, Sandbox, and Docker Learning MaterialsWhile shipping all these features, I also managed to prepare a bunch of learning materials 🤯 Not listing all of them here, but the last 15-ish Challenges in the Official Collection were added in April. And I also started working on a Firecracker course (thanks to the nested virtualization support), sharing my experience from 3 years of running iximiuz Labs. Here is the first lesson, and I'll definitely have a dedicated newsletter issue about it, too.
iximiuz Labs community updateThe community has also been busy! Nick Taylor published a tutorial on Pomerium - an open source identity-aware access proxy that lets you put identity-aware access control in front of any SSH server (with no tunnels or custom clients, which is slick). The tutorial walks you through a complete setup with a self-hosted authentication service and a GitHub OAuth app as the identity provider, running entirely in Docker. Teodor Podobnik continued methodically covering eBPF network programming topics - and each of his tutorials is a unique gem (despite somewhat look-alike titles 🙈):
Kaloyan Preslavski, our debuting author, prepared four Kubernetes challenges, and I particularly like how crisp they are - to the point, and yet there is enough guidance and learning opportunities on the way:
Last but not least, Omkar Shelke crashed it again with another portion of CKA/CKAD/CKS-styled Kubernetes challenges 👏
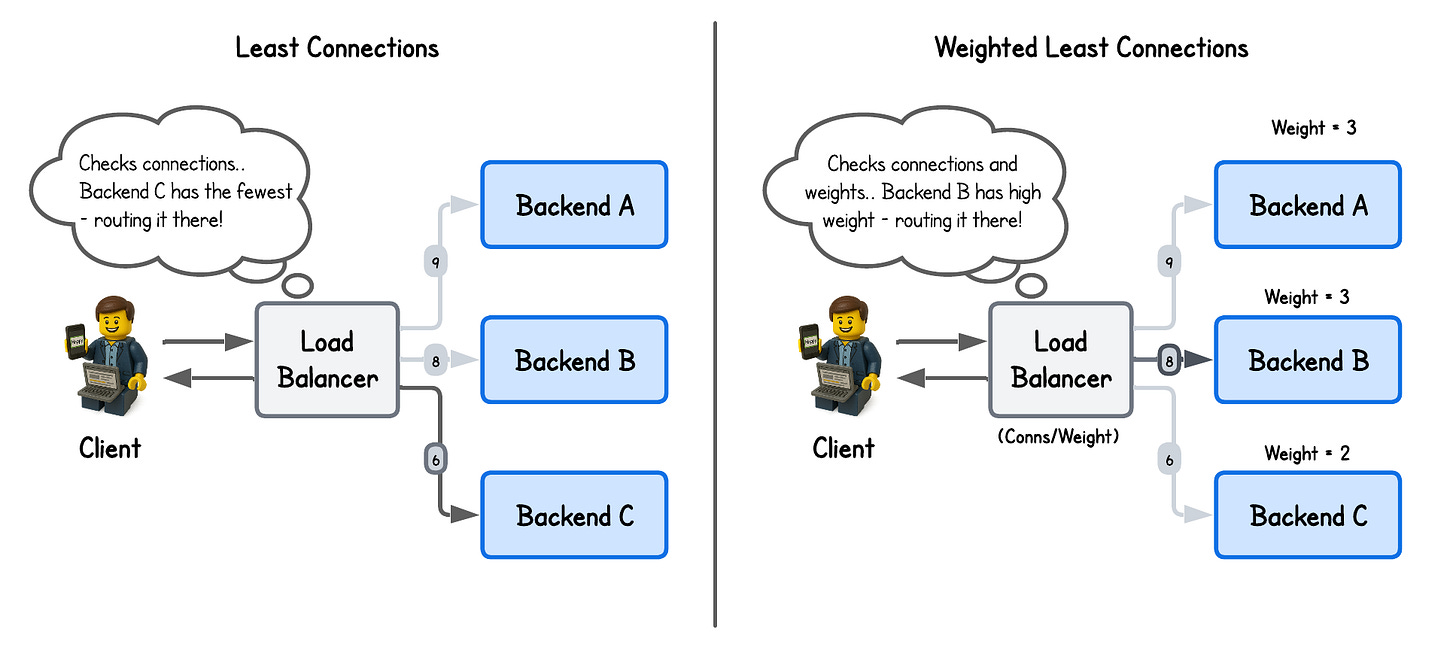
What I was readingThe invisible engineering behind Lambda's network by Werner Vogels - a pretty dense read, full of networking terms, that tells the story of the AWS Lambda cold start latency optimization. Interestingly enough, the better part of it sounds way too familiar - iximiuz Labs (obviously) isn't as optimized as Lambda, but it does use the same set of technologies under the hood (microVMs, network namespaces, veth pairs, iptables for NAT and traffic isolation, etc.), and it also started with all of these resources created on the hot path and gradually moving to warm pooling. By the way, solving iximiuz Labs networking challenges (veth, netns, NAT) would help you understand this post at least, or perhaps even apply for a network engineer position at AWS. Ubuntu 26.04 can install APT packages from GitHub Container Registry by Akihiro Suda - Everything has blended - container registries can now be used to distribute OS packages. The title of the post is a bit too narrow. What has actually just become possible is to Kubernetes 1.36: VolumeSource: OCI Artifact and/or Image is also GA - …and Kubernetes can now mount OCI images as volumes. At that pace, container images will soon become a more popular technology than containers themselves (especially since containers are in direct competition with more isolated runtimes like microVMs). By the way, if you want to learn how OCI images work, I've got a deep dive for you. Kubernetes v1.36: User Namespaces in Kubernetes are finally GA - That's it, that's the post. It took Kubernetes (well, more like Linux kernel and the container ecosystem) 10 years to come to this point. But that's an important milestone. A field guide to sandboxes for AI - A solid piece on sandboxing tech. I particularly liked how systematic the author is. They classify the available solutions into containers, userspace kernel (e.g., gVisor), microVM, and embedded sandboxes (e.g., Wasm), and then go over the strengths and weaknesses of each type. Plus, they also differentiate between "isolation boundaries" and "policies" - because even the strongest boundaries may not prevent a breakout if the right policies aren't in place. What every dev should know about AI sandboxes - A complementary to the above post. It's more shallow, and the opening part can feel like a rehash of the first post (which may or may not be the case). But it is helpful both as a quick recap and also because it expands on higher-level topics like agent observability, agent-to-agent communication, and the changing threat model. How will AI change operating systems? Part 1: Ubuntu and Linux - The Pragmatic Engineer - This is actually an interesting one. Windows and macOS are "obvious" options for AI adoption on the OS level. Cannot say I'm looking forward to Apple Intelligence taking over control of my devices, but sooner or later, they will force it on us. And it's a relief to hear that Linux distros seem to be taking a more pragmatic route. For instance, in the case of Ubuntu, AI adoption boils down to better hardware support (via improved drivers), focus on local inference, and OS-native agent sandboxing. OS-native agentic workflows are on the radar, but it's still in the research and experimentation phase. Wrapping upThat's it for April! Hope you find something useful in this update 🙌 Ah, and before we go, the pricing pilot is still live. I'm testing lower price points (40% off original prices + regional PPP discount) for all plans to better understand what makes iximiuz Labs sustainable while allowing as many learners as possible to use the platform. The pilot prices are temporary and may change once the test ends, but subscriptions started during the pilot will keep their lower prices indefinitely. If you wanted to upgrade your membership, now is a good time. Cheers Ivan |
Ivan on the Server Side
A satellite project of labs.iximiuz.com - an indie learning platform to master Linux, Containers, and Kubernetes the hands-on way 🚀